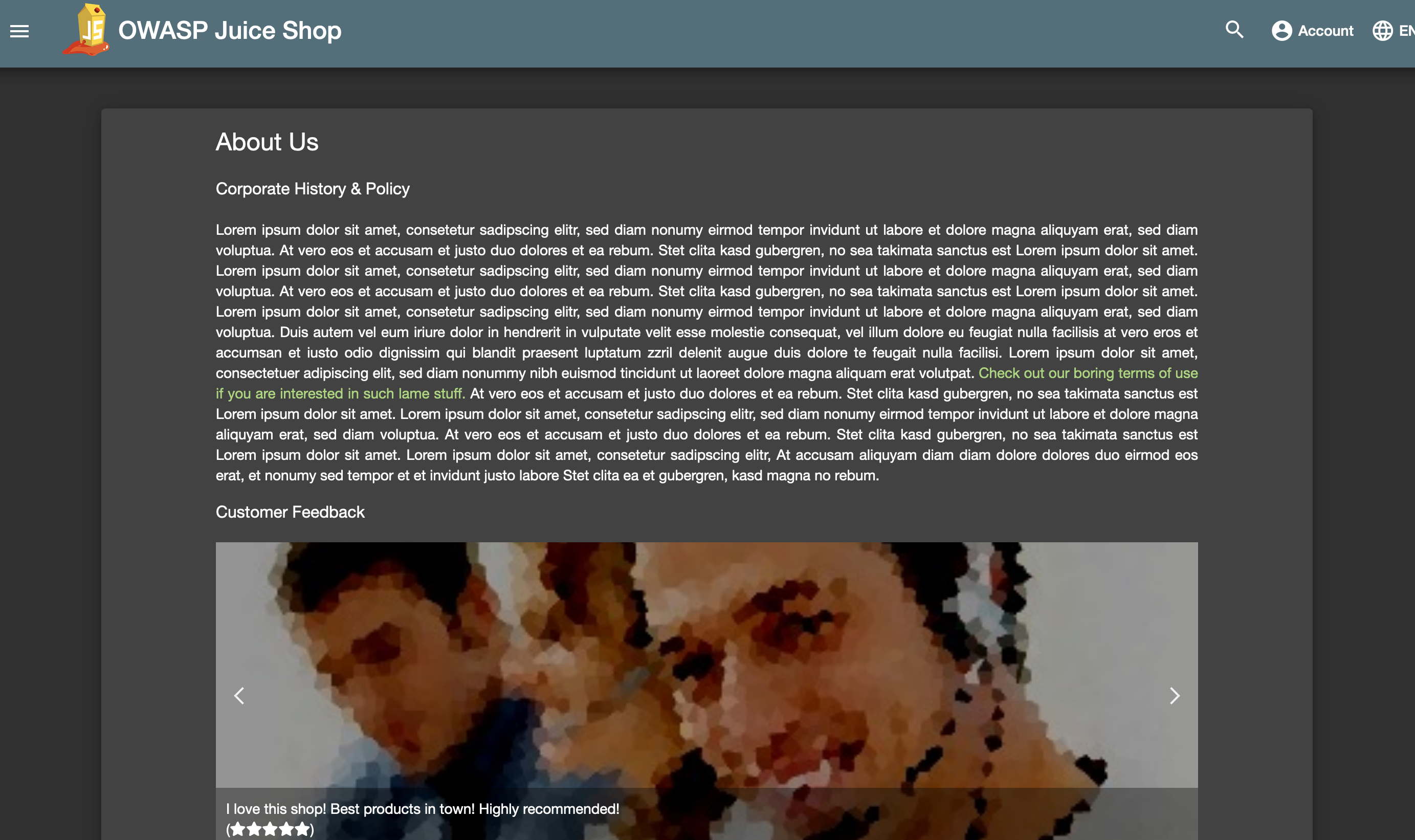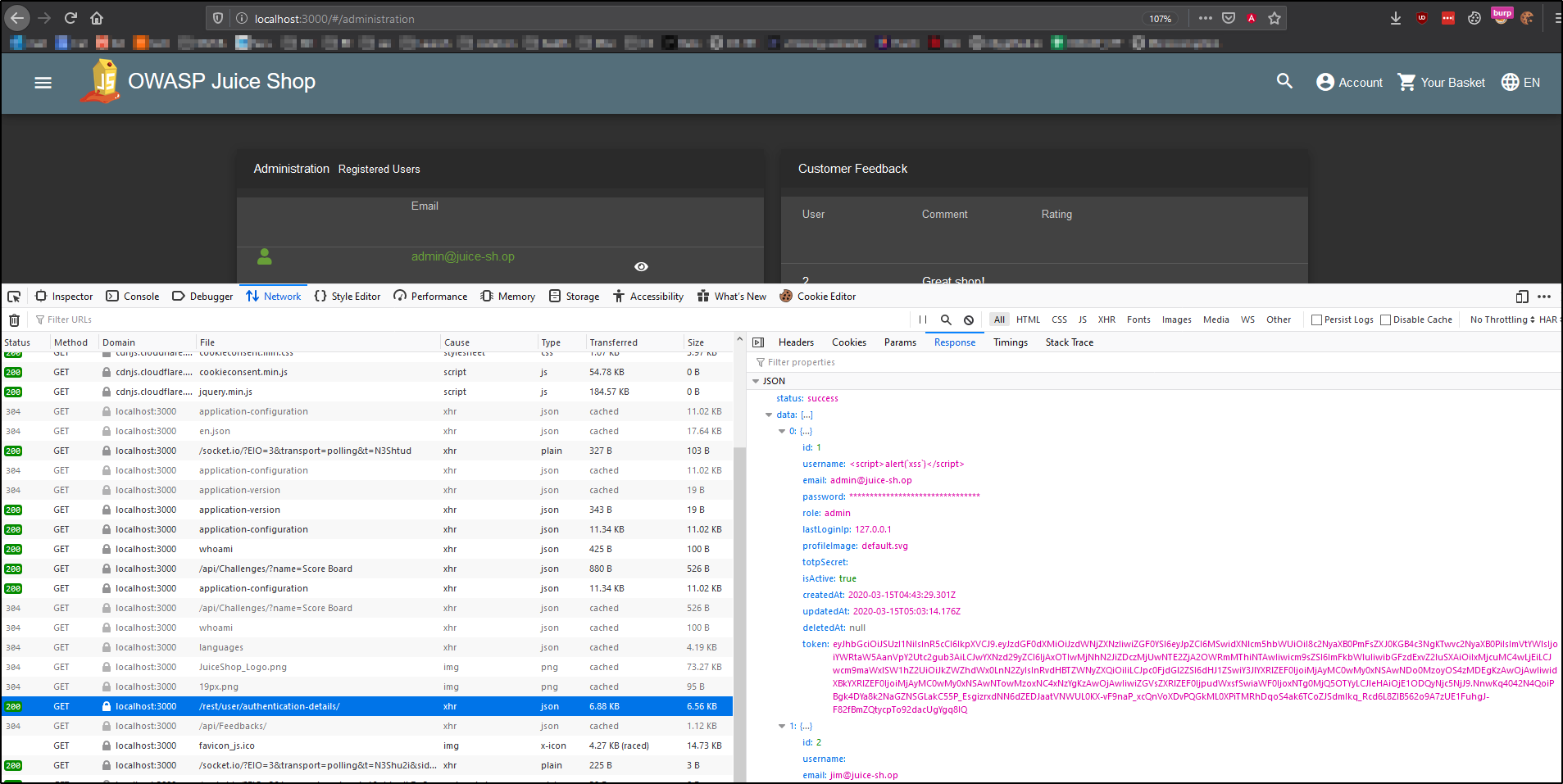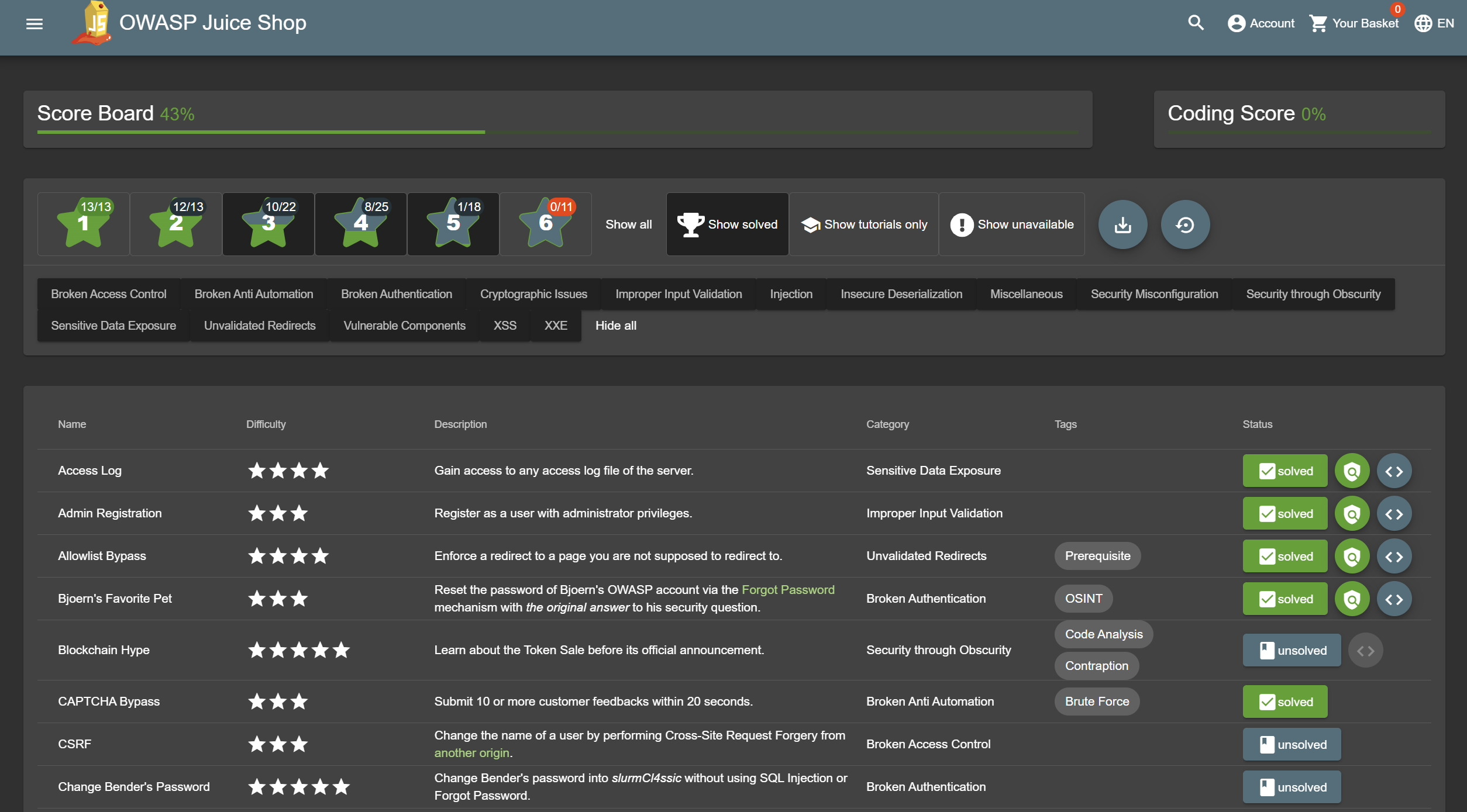
Beginner's Guide to OWASP Juice Shop, Your Practice Hacking Grounds for the 10 Most Common Web App Vulnerabilities « Null Byte :: WonderHowTo

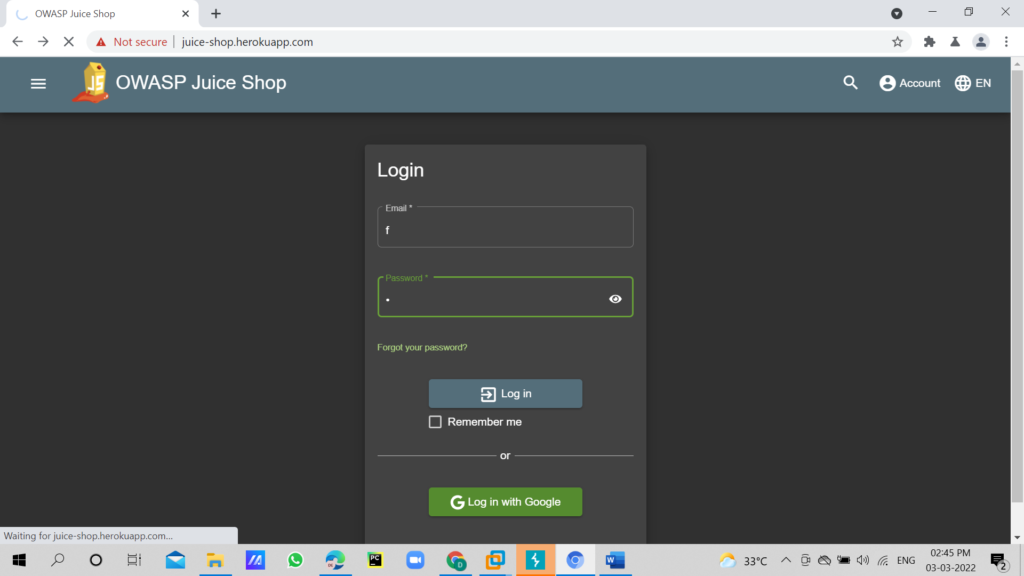
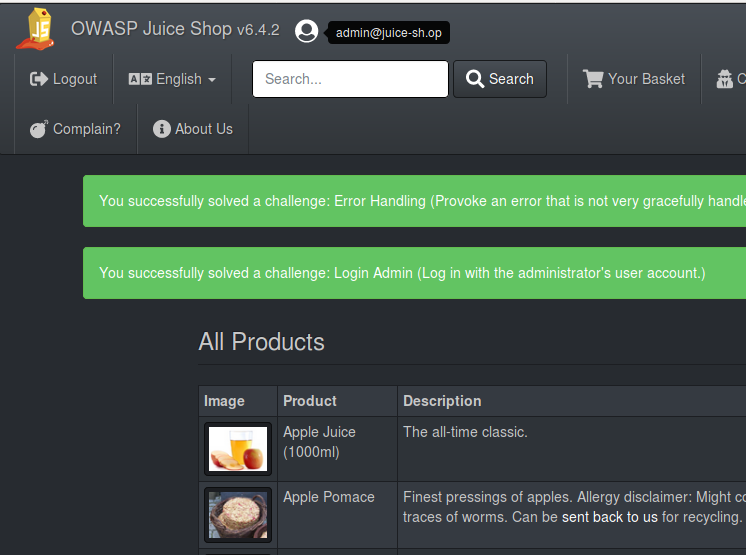
OWASP juice-shop | Log in with the administrator's user account | Injection | walkthrough ep-4 - YouTube

OWASP Top 10 Web application Application security Vulnerability, juice, logo, web Application, fruit Nut png | PNGWing
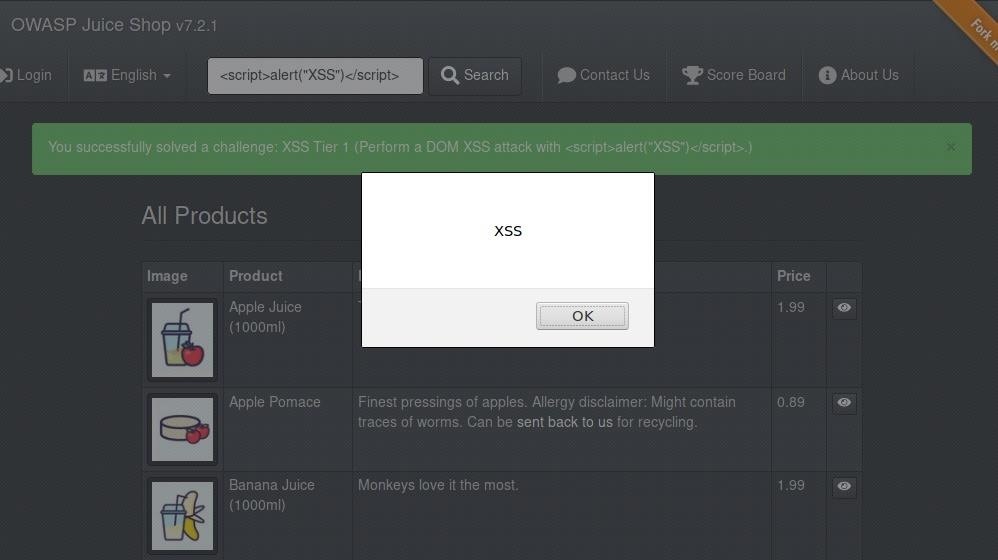
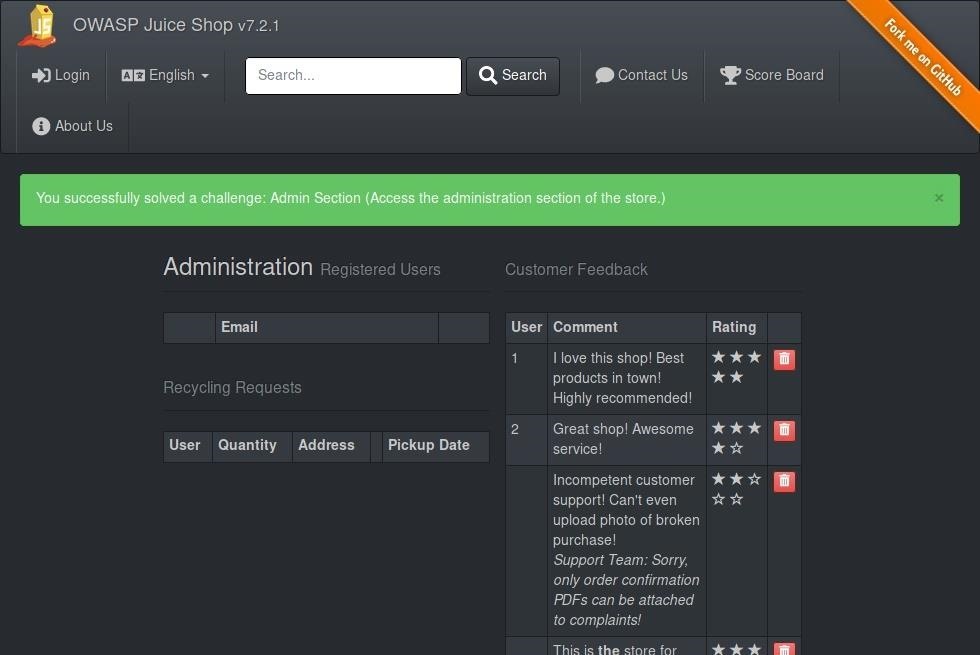
Beginner's Guide to OWASP Juice Shop, Your Practice Hacking Grounds for the 10 Most Common Web App Vulnerabilities « Null Byte :: WonderHowTo